This “Guide to Access Control” helps readers understand access control from its simplest definition to its most complex concepts and components. Whether you’re a beginner who is new to understanding access control or an advanced IT professional looking to delve deeper into technological advancements, this access control guide is for you.
READ MORE: Best Access Control Systems for 2021
Section I: Access Control Concepts
Components of Access Control Solutions
Why Is Access Control Important?
How Does Cloud Based Access Control Work?
How Access Control Works to Secure Your Premises
What Is an Access Control Policy?
Section II: Access Control Systems and Components
Check out Also:
What Is Access Control?
In its most basic sense, access control is any method of preventing unauthorized entry. Commonly used in the security industry, access control is a technology enabled method for preventing and permitting entry through a door, building, or system. It guarantees users have the appropriate access permission to an organization’s data or premises. Some access control systems (ACS) such as those that use biometrics, also authenticate users, which means they establish that users are who they say they are.
Access control systems keep buildings safe and secure by authorizing specific types of access for designated users. They allow security managers, admins, and receptionists to secure restricted areas and keep track of who enters and leaves specific parts of the premises.
Components of Access Control Solutions
Entry access control systems vary in design, organization, and method of operation. Most systems, however, share the following basic parts: readers, infrastructure, and software.
Readers
Installed near doors to capture user data for authentication and authorization, readers allow access via credentials such as key cards, mobile phones, and biometrics.
Infrastructure
The hardware (door controllers) and network that serves as the backbone of the system, infrastructure ties everything together. It connects the software, readers, and locks as part of one system. It also includes the electronics panels installers inside a server room, to control door lock release when someone is granted access.
Software
The brains of the system, software processes information and ensures the system works smoothly. It should present an intuitive interface for both system administrators and front-end users. Legacy access control systems typically run on servers inside a building, and newer systems run their software on servers remotely, in the cloud.
Why Is Access Control Important?
IT managers invest a lot of time and effort into logical access controls. These protect customer data, database storage, client contracts, intellectual property, and business documents. Physical access control is as important because it keeps employees, patrons, equipment, documents, hardware, and other important assets safe, and also tracks users’ access, reduces liability, and enables compliance.
Safety
Access control ensures the safety of data, equipment, people, and other assets in your organization. In fact, 50% of all commercial burglaries occur through an unsecured door. Physical access controls keep violent trespassers or visitors out of protected areas. This keeps staff, clients, and approved visitors safe. Logical access controls aid safety by keeping predators out of employees’ computers. Enterprise-grade solutions (like Swiftlane) provide integrated access management for both physical and logical systems.
Peace of mind
For building owners and property managers, it’s critical to ensure employees and tenants feel safe and secure. Implementing an access control system provides tools and solutions to create welcoming, safe environments.
Liability
Physical and logical access control systems reduce business risks by protecting assets. They also help fulfill the organization’s duty of care to protect employees, contractors, visitors, and others. These systems can help cut down on charges of premises liability, such as if an intruder enters an unprotected door at a factory and gets injured. These systems, as part of a solid security program, may also reduce insurance premiums.
Compliance
Organizations in regulated industries may need to install access control by law. In the U.S., this includes banking, nuclear plants, agricultural production, healthcare, and universities. Regulations like SOX for financial institutions and NERC for utilities require strong physical security systems and policies. Other examples are the HIPAA security rule (for healthcare providers, PCI regulations (for banking and insurance), and SOC2 cybersecurity standards (for SaaS providers). A robust entry point access control platform helps organizations comply with various regulatory requirements.
How Does Cloud-Based Access Control Work?
A cloud-based access control system does not involve running any large servers inside the building. Cloud software runs on a large fleet of servers remotely, inside data centers, and connects to your readers and devices over the internet.
A cloud-based ACS sits in the cloud. This allows organizations to promptly deploy an access control security solution without having to invest in expensive IT infrastructure. The system provides centralized management and control. Administrators and business owners can control the system from anywhere, at any time. The cloud platform is often owned and operated by a third party, so companies don’t incur purchase and maintenance costs.
Benefits of a Cloud-Based Access Control System
Cost Savings
A single cloud server can handle requests from hundreds of readers and buildings. Huge savings on expensive equipment inside the building.
Scalability
Ability to offload computation to large number of machines as needed, instead of on a single machine on-premise.
Higher Security
Cloud based systems offer significantly higher security for your data and systems. On premise systems run on traditional legacy laptops which can have many known security risks.
Read our full blog post about the 10 Benefits of Cloud Based Access Control.
How Access Control Works to Secure Your Doors and Buildings
Step 1
Users present their credentials (such as mobile phone, key card, passcode, or biometric data) to the reader at the point of entry. The reader sends the user’s unique code to the system for processing.
Step 2
The system authenticates the credential and checks whether the user has permission to enter. If so, it sends a signal – through the network infrastructure – to open the door.
Step 3
The software enables communication between the various hardware devices. Administrators can manage processes, such as adding or revoking users, and permitting access to specific locations at specific times. The software also keeps a record of who enters the building for monitoring and audit.
What Is an Access Control Policy?
Access control is critical to the security of buildings and facilities. Different organizations have varying needs and safety goals. An access control policy is a collection of principles that outline how access controls should be implemented. It sets the rules for determining who gets in and out and ensures proper compliance and regulations are followed.
What Is the Purpose of an Access Control Policy?
- Protect people and assets
- Ensure compliance with laws, regulations, standards, and certifications
- Audit pedestrian traffic
- Help trace violations or crimes to the perpetrator
- Monitor occupancy for mustering or in case of emergency or evacuation
What Questions Should an Access Control Policy Answer?
- Who may access your company’s premises?
- How do you make sure that those who attempt access have authorization?
- Under which circumstances do you deny access to a user with access privileges?
The policy should explicitly define its purpose, specify whom it covers, assign responsibility for oversight, specify use of the data and privacy measures in place, and explain how the policy will be enforced,
A good policy should change dynamically to respond to evolving risk factors. For example, an organization that has been breached should adjust its policies as necessary to prevent a recurrence. This would be crucial to reduce further business risks.
Methodology: Phases of Access Control
Today’s best practices might be tomorrow’s security failures. Understanding the underlying principles is crucial for optimal access control implementation.
The phases below represent the checks and controls that govern the functioning of an ACS.
Authorize
The first step in access control is authorizing the users. This means defining a set of rules and assigning specific privileges to users. For example, an office worker may receive 9 a.m. to 5 p.m. access to main entryways, bathroom doors, and the kitchen, while a systems administrator might receive 24/7 access to the same doors, plus server and storage rooms. Authorizing the system administrator to access server room doors, for example, is an example of role-based access control.
Authenticate
The next step is to authenticate the user. This requires a user to present a credential, such as a passcode, biometric, card key, or smartphone, which the system then must validate before permitting entry. In Swiftlane’s case, a credential can be a face, signal from a smart phone or a key card.
Access
If the user is authenticated and authorized, the system sends a signal to the door controller. A good ACS will open the door for a few seconds, long enough for the user to enter but short enough that someone can’t tailgate when the valid user is out of view. Access is granted by connecting an electronic door lock, to a hardware access control panel, which releases the door lock on successful access grant. This way, they allow fluid movement of people in and out of your premises.
Manage Every ACS provides the ability to manage access for users and define detailed permissions for various groups of users. A company might have high security areas that only specific individuals can access. The lobby area could be available to be accessed by contractors only from 9 am to 5 p.m. These are all examples of creating and managing access control. ACS provide the ability to create fine grained permissions and rules to ensure only the right authorized individuals can access various entry points.
Audit
In case of a breach or a security incident, the entry access control system is the first place to look. Administrators should have round-the-clock access to investigate events. This makes it possible – and easier – to monitor employee movement and behavior at all times of the day. In addition, audits provide evidence of compliance with relevant rules and regulations, such as GDPR, HIPAA, PCI, as well as ISO, UL, or ANSI standards.
Three Types of Access Control
The process of deploying an ACS looks different for each organization. Many factors influence the decision. These factors include: the nature of data, relevant standards or regulations, organizational culture, types and scope of risk, and the size of the business. Many options exist for organizing and managing your access control system; three types are most common.
Role Based
In a Role Based Access Control (RBAC) system, an administrator delegates access privileges based on the employee’s position and duties. This type of access control makes it easy to assign permissions based on job titles and descriptions. If an employee is promoted to “supervisor,” then their access credentials are upgraded to supervisor level. RBAC is popular in the business world since it has a clear set of guidelines, reduces administrative work, and maximizes operational efficiency. These roles can be translated into logical roles inside an access control system, and we can add users into each “role”, to automatically grant the permissions associated with that role.
Mandatory
In a Mandatory Access Control (MAC) system, all end-users are classified and assigned labels. These labels allow them to gain access pursuant to established guidelines. It is impossible for the end users to change permissions that grant or bar entry to different areas within the facility. MAC is popular in entities that need strict confidentiality and stringent classification of data. Examples include military institutions and other government entities
Discretionary
Discretionary Access Control (DAC) is the default option for most access control systems. In this setup, the business owner makes their own decision on who can access what areas in their facility. Each door (entry point) is programmed with a list of individual users or groups of users who have permission to enter. DAC is less restrictive than other types of access control. A user with certain access permission can pass their permission on to another user. A key benefit of DAC is that it offers more flexibility, efficiency, and cost-effectiveness, but at the expense of being less secure.
Doors, locks, cards, and readers are the most obvious physical components of an access control system, but other key hardware is less obvious. This piece explains the function of each component of an access control system.
Access Control Hardware
Doors, locks, cards, and readers are the most obvious physical components of an access control system, but other key hardware is less obvious. This piece explains the function of each component of an access control system.
10 Basic Components of an Electronic Access Control System
Doors
Steel, fiberglass, wood, aluminum, and glass are the major types, with issues such as price, security, ease of installation, environment, and company culture among factors to consider.
Door locks/strikes
The most common types of locks used in electronic access control are electromagnetic locks and electric strike locks.
Electromagnetic locks consist of an electromagnet attached to the top of a door frame and an armature plate (that is, a plate to which a magnet sticks) attached to the door.
Electric strike locks are mechanical locks that use electronic components.
Request to exit devices
Request to Exit (REX) devices allow people within an access controlled area to exit the space without having to use a credential, keypad, or other means.
Motion sensors
REX devices almost always use infrared technology for their sensors. Passive infrared sensors detect heat and unlock the door in response to change in temperature.
Active infrared sensors have both an emitter and a receiver. If the sensor beam is broken by an object, such as a person, it triggers the door to unlock.
Readers
Installed at protected access points, they “read” some input, such as a card, a face, a mobile phone, or a signature, and they forward the information to a control panel.
Keypads
Keypads serve a similar purpose as readers. They receive an input that enables a user to enter a controlled space. They are a low-security option.
Panels/Controllers
Often located in telephone or electrical closets, access control panels pull together all of the hardware.
Servers
The server assigns access to and tracks traffic through access points. Besides holding a database of permissioned users and their access levels, it retrieves access control data from each panel.
Cables/Wiring
Many access control systems, especially legacy systems, rely on cables to transport data. Even wireless systems often use some wiring.
Power Supply
Access control systems often require their own power supply. These help reduce the power delivered from the electric utility to a form that an access control system can accommodate.
Read more about Access Control Hardware here.
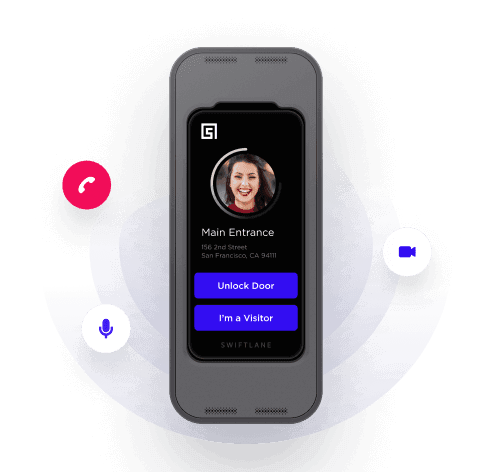
Mobile Access Control
The prevalence of cellphones, tablets, and similar devices has triggered the growth of mobile access control: these devices replace cards as access tokens. Mobile devices offer many advantages over their plastic counterparts. Phones are more convenient to carry, they are more secure, there are no replacement or reprinting costs, and eliminating key cards means one less object to touch during a pandemic. As powerful computers, mobile devices are beginning to be used for functions akin to access control, such as mass notification, presence detection, and virtual buttons.
Mobile devices connect to readers via two types of technologies. Near Field Communication (NFC) offers secure, short-range communication between compatible devices. Although this technology is efficient and secure, it doesn’t match the strength, flexibility, and popularity of Bluetooth. Bluetooth Low Energy (BLE) is a widely used standard that offers much longer read ranges; however, improperly configured readers may open the wrong door.
Both startups and mature providers alike have rushed to meet the demand for mobile access control, introducing apps that permit users to unlock doors via smart devices, Swiftlane Mobile Unlock delivers a reliable, seamless experience, using either Bluetooth Low Energy or cellular service. Unlike other systems, signals are encrypted for high security, and the efficient operating system preserves phone battery life.
Read the full Guide to Mobile Access Control here.
Need More Info?
Still have questions about the best access control for your facility? Contact a Swiftlane expert to navigate your options and the best solution.