In this article, you will get a complete overview of key card entry systems, and key card formats. Swiftlane, a provider of modern, cloud-based access control systems, has put together a guide to access card technologies that exist today. Use this guide to understand access card formats, their pros and cons, and evaluate your key card system needs.
How Key Cards Entry System Work
Keys, throughout their technological evolution, have taken many forms. As such, so have key card access control systems as a whole.
For example, some of you may use a fob to get into your parking garage. Others may have a key card with your picture on it to get into your office building. When you go to a hotel, there is a good chance you will swipe a magnetic stripe card to get into your room.
Yep, these are all key cards.
The purpose is the same: to manage access to a particular area.
All key cards work through the same basic principle.
- A token (such as a plastic key card or fob) is presented to an electronic access control device called a reader
- The key card stores digital credentials in the form of an electronic code
- The data may be stored and transmitted over a Wiegand wire, an RFID microchip, or a magnetic stripe
- The reader reads the code when the key card is swiped or placed close to it and sends the data to a controller
- The controller compares the received credentials with its database and sends a signal to the electronic lock depending upon the match type
- Access is granted by remotely unlocking the door when there’s a positive match; or restricted when there’s no match
Types of Key Card Entry Systems
Key cards can be divided into different types depending on the technology they use to store data and communicate with the reader.
- RFID Key Cards
- Proximity Cards
- Smart Cards
- NFC Key Cards and Emulators
- Hybrid Key Cards
- Wiegand Cards
- Magnetic Stripe Cards
RFID Key Cards
RFID stands for “radio frequency identification.” Data is stored in a microchip often referred to as an RFID tag. RFID cards have many variants, especially when it comes to key card entry systems. In fact, all key cards other than Wiegand and Magstripe use RFID technology to transfer data to the reader, but they have different working mechanisms.
Technology: RFID technology uses RF waves to read and transfer data. The RFID frequency bands utilized in cards include 125 kHz low frequency for proximity cards, 13.56 MHz high frequency for smart cards, and 860-960 MHz ultra-high frequency (UHF) for high range applications.
Applications: RFID cards, badges and tokens are used in an extensive range of diversified applications including key card access control systems, logistics and supply chain management, inventory and asset tracking, materials management, animal tracking, ticketing, marketing, healthcare, law enforcement, and more.
Printing and Encoding: RFID cards can be printed on using a printer similar to swipe card printers. Some of them can be encoded by the user while others may come precoded by the provider. RFID tags contain memory banks that can store varying amounts of data, from 96 bits or 128 bits (for license plate tags) to 64,000 bits (for high-security access control applications).
Advantages
- Reduce the human effort and errors compared to pen and paper access control systems
- Dont require line of sight to be read
- RFID readers can read multiple RFID tags simultaneously
- Don’t need to be swiped or inserted into the reader. Certain types of RFID cards are contactless, such as smart cards.
Limitations
- The RF signal can be encrypted, but most RFID cards do not have encryption.
- Typical RFID cards and readers don’t have mutual authentication, which means anyone who is within range and has a reader can extract the information stored in the key card
- Most RFID cards are easy to clone
Contactless Cards for Access Control
There are three types of contactless cards or badges for key card entry systems. These can be read from a distance and do not need to be inserted into the reader. All of them use RFID protocols but use different technologies to store and read data. They are proximity cards, smart cards, and NFC cards.
Proximity Cards
Proximity cards, sometimes called Proxcards or smart cards, are low frequency RFID cards and badges, which do not need to be inserted into the reader like swipe cards. Proximity cards typically work on 125 kHz LF band. These are read-only, contactless cards or badges that can store a limited amount of information.
Typical proximity cards can be read from a range of up to 15 inches (<50 cm). Their advantages, limitations and way of working are the same as RFID cards, except that they do not need to be inserted in a reader.
Smart Cards
Smart cards include a microcontroller instead of an RFID interface. Contactless smart cards can be read from a distance of up to 4 inches (10 centimeters). Typical smart cards have 8k storage capacity and 8-bit computing power.
Technology: The smart card secure microcontroller is an intelligent device that can perform complex functions; such as managing, storing, encrypting, and providing secure access to data. The technology also allows the card to authenticate the reader and prove its own authenticity, which makes smart cards more secure than RFID tags as they function in key card access control systems.
Security: The information stored in the smart card as well as the communication between the smart card and the reader can be encrypted. Smart cards are very difficult to duplicate and include a variety of hardware and software capabilities to detect and react against tampering attempts. The smart card can verify the authority of the device requesting the information and then give access to only the authorized information.
Applications: Smart cards are used in applications that require a higher degree of information and communication security, such as banking, government IDs, and passports as well as key cards and fobs for entry into secure facilities.
Encoding: The data and information on smart cards can be read, written or modified using advanced ID card software. A smart card reader can be connected with a computer through a USB cable and the data on the card can be used for access management and security applications.
Advantages
- More secure than RFID and swipe cards because of encryption and mutual authentication features
- Can work from a distance and provide touchless functionality
- Some advanced types (such as optical cards) can store several MBs of data
- Overcomes limitations of 125 Khz proximity cards, which are easy to clone
Limitations
- While most smart cards cannot be cloned or forged, they can still be lost, misplaced, stolen, or forgotten
- High frequency cards can be expensive compared to prox card or mobile phone based credentials.
- Higher lock-in: Unfortunately, since these cards use proprietary key card encryption, there is a strong lock-in to a card reader and card provider.
NFC Key Cards and Devices
NFC (Near Field Communication) cards, sometimes also called NFC smart cards, can be read using a smartphone or another NFC-enabled device. These cards contain a writable NFC chip that can be used to read and store messages, numbers, and other microdata using a NFC enabled smartphone.
Technology: NFC cards communicate through radio frequency signals. In that sense they’re also RFID cards. The main difference from RFID cards is that a NFC device can act as a tag and emulate a card. NFC operates on HF 13.56MHz frequency band.
Applications: NFC technology is used for contactless payments, access control, embedded advertising, loyalty programs, Internet of Things, workforce management, and numerous other applications.
Access Control: For secure access control purposes, any NFC mobile device can be configured to emulate a key card entry system and can be used to access a facility. The user has to touch the NFC token with the NFC reader, or bring it within 0.39 inches (<4cm) of the reader, for the data to be read. NFC is sometimes used in combination with Bluetooth and WiFi to boost the speed of data transfer between the NFC card emulator and the reader.
Advantages
- The main advantage over RFID is that NFC cards can be read with NFC enabled smartphone or PC
- NFC devices can emulate access control cards. Many mobile access control systems use NFC technology
Limitations
- NFC is more secure than regular RFID cards, but can be hacked if an attacker succeeds in breaking into your phone or computer
- Another limitation is the slow rate of data transfer compared to Bluetooth, WiFi, and microprocessor-based, contactless smart cards
Proximity Cards Vs Smart Cards Vs NFC Cards
Proximity cards, chip-based smart cards, and NFC cards are all contactless cards that can be read without inserting the card into a reader. All of them are used in physical access control, but there’s a difference in the way they work.
| Proximity Cards | 13.56 Mhz Smart Cards | NFC Cards |
| Read distance (air interface) up to 15 inches | Read range up to 4 inches | Read range up to 4cm |
| Most of them are passive cards that do not transmit | Can be passive or active cards with a transmitter | Can be passive or active |
| Contain an RFID tag | Contain an intelligent microcontroller | Contain a NFC tag |
| Most are read-only cards | Can be read or written to | Read and write |
| No encryption | Data can be encrypted using algorithms | Can support encryption |
| Store only facility code and card number | Can store facility code, card number, biographical info, pin codes, or monetary values in addition to facility code and card number | Can store customizable data that can be used by a computer for applications such as PIN code verification or to launch an app |
| Cannot authenticate the device requesting the information | Can authenticate the device asking for the info and provide only the data for which that particular device is authorized | Can verify the asker’s identity before transmitting the data |
| Work on LF 125kH | HF 13.56MHz | HF 13.56 |
| RFID Reader | Smart Reader | NFC Reader |
| Cheapest Option | More expensive but secure | More expensive but secure |
Hybrid Key Cards
Hybrid key cards use a combination of technologies to enable a number of specific applications. For example, a magnetic stripe card can include a smart chip, where the stripe can be used for key card access control systems and the chip can be used for storing account information and withdrawing funds or making purchases. Contact-based and contactless smart cards or UHF and LF can be combined to deliver more flexibility usage, particularly as it pertains to key card entry systems.

Wiegand Key Cards
Not to be confused with Wiegand card format for transmitting data in access control systems, Wiegand cards are based on a magnetic phenomenon called the Wiegand Effect. They use low-carbon Vicalloy, a ferromagnetic alloy of cobalt, iron, and vanadium, to store a unique number that can be read by a Wiegand reader. Filaments of Wiegand wire are embedded in a plastic key card to create a unique binary code that is tied to a specific person or item. Wiegand Cards were the earliest version of key cards and were introduced in the 1970s. They continue to be used to this day because of their simplicity and durability
The Wiegand Effect: In 1970, American inventor and musician John Wiegand discovered that when a specially treated piece of ferromagnetic alloy (the Wiegand wire) is exposed to a reversing magnetic field, it abruptly flips to opposite polarity within a few microseconds.
Early Applications of Wiegand Cards: The early version of plastic key cards had short lengths of Wiegand wire embedded into it. The wires were arranged in an array that represented a binary number. The presence of a wire would mean a 1 and an empty slot represented a 0.
Reading the Wiegand Card: When the card is swiped through a reader, it is exposed to a magnetic field, which triggers the polarity reversal in the embedded Wiegand wire. The reader detects the polarity reversal and can hence read the unique binary number hard wired into the key card.
How Wiegand Cards are Encoded: Wiegand cards cannot be printed using a contemporary key card printer. The Wiegand wire filaments are permanently embedded in the card, making them impossible to duplicate.
Are Wiegand Cards Still in Use Today? Wiegand cards have been largely replaced by more advanced credential technologies such as Magstripe and RFID. However, legacy access control systems continue to use the Wiegand protocol as a wiring standard for readers and controllers.
Advantages
- Simplicity and ease of use
- Cannot be easily duplicated or cloned
- Have a longer life than Magstripe and RFID cards
Limitations
- Wiegand cards can only store a limited amount of information
- They cannot be written or programmed by applying magnetic fields
- Wiegand Protocol does not encrypt the data, so the data can be read by any Wiegand reader in the vicinity of the card
Magnetic Stripe Cards
A magnetic stripe card, sometimes also known as a swipe card or magstripe, records credentials by modifying the magnetism of tiny iron particles embedded in a stripe of magnetic material on the card.
Magnetic Recording Technology: Swipe cards store data using the 1960s magnetic recording technology used in audiotapes. When the card is swiped, the data stored on the magnetic stripe is read by a magnetic head similar to those used in old cassette players.
Applications of Magstripe Cards: Developed by IBM almost 50 years ago, swipe cards are still being used in credit cards, identification badges, hotel key cards, loyalty cards, and transportation tickets.
How Swipe Cards are Encoded: Organizations can print and encode their own cards using magnetic stripe cardstock, ID software, and an ID card printer with a magnetic encoder.
Advantages
- The main advantage is that the data on the magnetic stripe can be encoded after the card has been manufactured
- A swipe card can also hold more data than a typical Wiegand card
Limitations
- Magnetic swipe cards require physical insertion into the reader and are likely to wear out sooner than contactless cards
- The data on them can be damaged by stray magnetic fields
Choosing a Key Card Entry System
Below are some considerations when choosing a key card entry system for your facility.
Cheapest Install
Use low frequency prox cards for lowest installation cost. These key card entry systems cost the least. However, they suffer from severe security risks in addition to high operational costs of replacing lost and stolen cards.
Best Key Cards
High frequency card formats, like 13.56 Mhz encrypted cards, offer high security as they cannot be replicated or cloned. These cards are more expensive and might require a more expensive reader to be installed as well. They also suffer from vendor lock-in often.
Modern Key Card Deployments
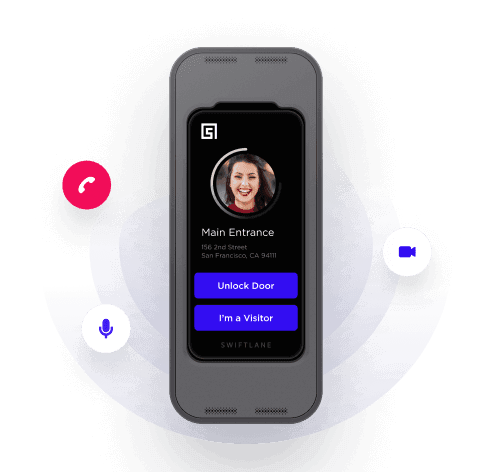
In 2020, mobile credentials are completely mainstream and most companies are looking to use smartphones for access. Face recognition is also being used for access to hundreds of millions of Apple phones via Face ID, and similar technology is ramping up for building access. Swiftlane provides a secure face recognition based access control along with its mobile credentials.
Alternatives to Key Card Entry Systems
A key card entry system was revolutionary at its inception. It offered more flexibility in its capabilities to access multiple sites and could be reconfigured as needed. However, as technology has progressed, so too has our capability of better and more secure solutions.
Drawback of Key Cards
Key cards are a legacy technology slowly losing the interest of those in the market for modern, durable solutions. To that point, with the advance of access control technology, key card entry systems are showing their limitations:
- Key cards, badges and key fobs can always be lost. The average 40,000-employee enterprise loses more than 10,000 cards each year
- Most cards can be hacked and cloned quite easily using cheap RFID readers
- It’s a pain to deactivate lost or expired cards and issue new cards
- The cost of creating and dispatching cards can be mind boggling
- Lost or misplaced cards are a looming security threat
Face Recognition Entry Systems
With advancements in the field of computer vision, face recognition access is becoming popular due to the high security and low friction for access.
Swiftlane’s cloud-based facial recognition solution is changing the way we view access control and security. As a cost effective and highly efficient option, Swiftlane offers a unique access control experience for all types of facilities.
Mobile Access Control Credentials
Cloud-based access control has made it possible to use the credentials on your phone for access. Mobile access control has eliminated the need for additional tokens (key cards, fobs, etc.) while leveraging the device that 93% of Americans have with them all the time.
Need More Info?
Still have questions about an access control system for your facility? Contact a Swiftlane expert to navigate your options and the best solution.