In today’s fast-paced and technology-driven world, securing our physical and digital assets is more crucial than ever. Access control systems play a significant role in making this possible, as they provide the means to protect sensitive information, resources, and properties from unauthorized access. The importance of access control cannot be overstated, and it has become an essential component of comprehensive security measures across a wide range of industries. In this blog post, we’ll look into the fascinating world of access control, exploring various types of systems and their applications for different sectors. So strap on in, and let’s embark on this security-centric journey together!
Table of contents
- Physical Access Control Systems
- Logical Access Control Systems
- Considerations for Choosing an Access Control System
- The Future of Access Control Systems
Suggested Posts:
- A Closer Look: The Future of Apartments
- Guide to Commercial Door Access Control
- Why Touchless Access Control Systems Are the Future
- Keyless Door Entry Systems in Commercial Buildings – An In-Depth Guide
Here’s a sneak peek at what we’ll be covering:
- Physical Access Control Systems: Discover the role that physical access control plays in securing buildings, facilities, and restricted areas. We’ll investigate various access control methods, such as key cards, fingerprint recognition, and electronic doors.
- Logical Access Control Systems: Learn about securing computer systems, networks, and databases through logical access control. We’ll discuss the different types of logical access control, including discretionary, mandatory, and role-based access control, and delve into various authentication methods.
- Considerations for Choosing an Access Control System: Get the low-down on what factors to keep in mind when selecting the perfect access control system for your needs. We’ll explore security requirements, scalability, ease of use, integration, and costs.
- The Future of Access Control Systems: Peek into the crystal ball for an exciting glimpse into emerging trends and technologies in the access control arena, such as IoT integration, machine learning algorithms, and the application of blockchain technology. Stay tuned, as we delve deeper into the realm of access control systems and embark on this enthralling voyage together!
Physical Access Control Systems

Physical access control systems play a vital role in securing buildings, facilities, and restricted areas by regulating who can enter and exit specific locations. These systems help prevent unauthorized access, protect valuable assets, and maintain the safety of employees and visitors alike. Let’s take a closer look at some popular access control methods:
Key Cards
- Widely used in offices, hotels, and gated communities.
- Convenient and easy to carry.
- Can be lost or stolen, which requires prompt deactivation.
Fingerprint Recognition
- Biometric technology that authenticates users based on their unique fingerprints.
- Difficult to duplicate or forge.
- May need regular maintenance for the scanner to function correctly.
Electronic Doors
- Controlled remotely or through access codes, key cards, or biometrics.
- Provides enhanced security and convenience.
- Expensive to install and maintain. Cloud-based vs. On-premise Security Systems There are also two main approaches to managing physical access control systems: cloud-based and on-premise solutions.Cloud-based Systems
- Easily scalable and accessible from anywhere.
- Reduced IT infrastructure costs.
- Data security depends on the provider.On-premise Systems
- More control over data security.
- May require additional investments in hardware and maintenance.
- Scalability can be limited.In conclusion, physical access control systems are integral to securing different types of properties and safeguarding sensitive areas. Choosing the right combination of access control methods and management approach is essential for optimal protection and convenience.
Logical Access Control Systems
In the world of cybersecurity, logical access control acts as the gatekeeper, safeguarding vulnerable digital assets like computer systems, networks, and databases. Let’s dive into the various types of logical access control systems and the ways they authenticate users.
Discretionary Access Control (DAC)
- A flexible and user-friendly system.
- Access rights are granted by the owner of the information.
- Real-world example: A manager deciding who can access specific company documents.
Mandatory Access Control (MAC)
- Robust and highly secure.
- Access rights are based on classification levels and user clearances.
- Real-world example: Military networks, where sensitive data needs to be tightly controlled.
Role-Based Access Control (RBAC)
- Highly customizable and adaptable.
- Access rights are based on predefined roles and responsibilities.
- Real-world example: Hospitals, where nurses and doctors can only access relevant patient data. Authentication Methods, let’s explore how user authentication occurs within logical access control systems:
- Passwords: The classic method, using a unique combination of characters.
- Biometrics: More secure, based on the user’s physical characteristics (e.g., fingerprint or facial recognition).
- Two-factor Authentication: Combining two methods for enhanced security (e.g., password + biometric). In short, logical access control systems secure digital assets and resources. Choosing the most suitable type depends on your security requirements and organizational structure.
Considerations for Choosing an Access Control System
Choosing the right access control system is crucial to ensure the security and efficiency of your organization. But with so many options available, how do you know which one is the best fit? Let’s discuss five key factors to consider when making your decision:
Security Requirements
- Assess the specific security risks and vulnerabilities your organization faces.
- Determine which features and access control methods will best address those risks.
Scalability
- Consider the growth and expansion potential of your organization.
- Ensure the system you select can adapt to increasing numbers of users, locations, and access points.
Ease of Use
- Check that the system is user-friendly, both for administrators and end-users.
- Look for intuitive interfaces, easy-to-understand features, and responsive support teams.
Integration with Other Systems
- Identify existing systems and platforms your organization uses, such as security cameras, HR software or visitor management systems.
- Make sure the access control system you select is compatible and can integrate seamlessly with these systems.
Cost
- Analyze initial investment costs, ongoing maintenance costs, and potential cost savings.
- Weigh the value of the system against your budget limitations. Evaluating Vendors and Implementation When evaluating vendors and planning for a successful implementation, keep these tips in mind:
- Request detailed product demonstrations and compare features.
- Seek customer reviews and testimonials.
- Look for vendor expertise in your industry.
- Assess the quality of installation, training, and ongoing support services. By carefully considering these factors, you’ll be well-equipped to choose the perfect access control system tailored to your organization’s unique needs.
The Future of Access Control Systems
As we look ahead, emerging trends and technologies are poised to revolutionize the access control industry. Let’s dive into some exciting innovations that have the potential to enhance security, user experience, and operational efficiency in both physical and logical access control systems:
IoT Integration
- Seamlessly connects multiple devices and systems, enabling intelligent access control solutions
- Offers real-time monitoring, analytics, and remote management capabilities
- Use case: Smart home security systems that manage access to various home devices and entry points
Machine Learning Algorithms
- Harnesses the power of artificial intelligence to analyze patterns and detect anomalies
- Enhances security by identifying potential threats and unauthorized access attempts
- Use case: Automated systems that detect and block unauthorized users based on their behavioral patterns
Blockchain Technology
- Employs a decentralized, tamper-proof digital ledger for secure data storage
- Enhances transparency and traceability of access events, reducing the risk of fraud
- Use case: Secure sharing of access credentials within a network, without a central authority. These advancements are shaping the future of access control, offering improved security, convenience, and efficiency. As these technologies continue to evolve, it’s essential for organizations to stay informed and adapt accordingly to remain at the forefront of access control innovation.
Conclusion
In conclusion, access control systems are essential for protecting both physical and digital assets. As we’ve explored throughout this blog post:
Physical Access Control Systems offer protection for buildings, facilities, and restricted areas using methods such as key cards, fingerprint recognition, and electronic doors.
Logical Access Control Systems secure valuable information in computer systems, networks, and databases, using techniques such as discretionary, mandatory, and role-based access control.
Choosing the right system requires considering factors like security needs, scalability, ease of use, integration, and cost.
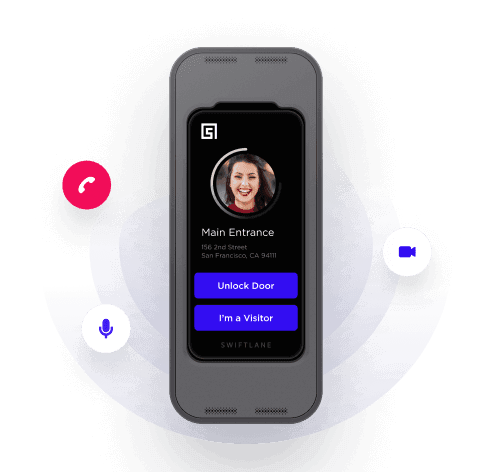
Check out how Swiftlane’s full array of access control products here:
The future of access control is brimming with exciting innovations, including IoT integration, machine learning algorithms, and blockchain technology. So, what’s next? It’s time to explore your options and find the perfect access control system that fits your unique security needs. For more information on access control systems and related security solutions, contact Swiftlane today. Our team is eager to help you navigate this critical aspect of safeguarding your organization’s assets. Don’t wait – secure your future now!
Upgrade Your Building Security
Get in touch with a Swiftlane specialist for more information on the best access control and video intercom solution for your building.