Physical access control solutions are changing rapidly. Features like remote management, cloud connectivity, and touchless entry have become top access control trends in 2023. This blog post will help you understand the factors involved in choosing an access control solution for your office or building.
Table of contents
- Key Factors to Consider for Selecting Access Control Solutions
- Factor 1: Your Access Control Needs
- Factor 2: Access Credential Type
- Factor 3: Access Management Experience
- Factor 4: Combining Occupant Access with Visitor Access
- Factor 5: Multi-Location and Hybrid-Office Access
- Additional Factors to Consider
Also, read
- Best Video Intercom Systems
- 30 Drawbacks of Key Card Systems
- Keyless Entry Systems for Apartments
- Apartment Intercom System with Door Release
- 10 Benefits of a Cloud-Based Access Control System

Key Factors to Consider for Selecting Access Control Solutions
Companies looking to buy access control solutions in 2023 should look beyond key cards and PIN codes. Today’s access control systems allow you to control access from anywhere through mobile devices. You can use not just cards and fobs, but also your smartphone or your face to gain entry into workplaces. With changing technology, the expectations of your residents or tenants are also changing. Let’s look at the factors you should consider to create a safe and welcoming workplace.
You may also like to read: The Best Access Control Systems of 2022
Factor 1: Your Access Control Needs
Thanks to the advancements in technology, modern cloud-based access control systems can address all of your needs. However, you must know what those needs are. Here’s some thought appetizers to get you started.
Remote Working Needs
According to the latest surveys, more than half of workers (55%) say they work more hours remotely than at a physical office. If your workforce includes remote or hybrid workers, you cannot expect them to come to the office every other day to pick up a badge.
Multiple Office Locations
Companies are opening satellite offices to balance remote work with networking and face-to-face team interactions. If you have to manage multiple branch offices, you’ll need the ability to grant and revoke access remotely across multiple geographically distant locations.
Visitor Management Needs
Offices that receive customers, visitors or deliveries need to look for a way for occupants or security to speak to visitors via audio or video calling even from outside their offices or and release the door remotely.
Security Needs
One of the obvious factors is the number of doors and users you want to secure. The needs of a large commercial building are different from those of a small single location office.
You won’t be changing your newly installed access control system anytime soon, so make sure you understand the needs of your workers and select the best-fit solution.
Factor 2: Access Credential Type
The types of physical access control credentials that various systems use include keycards and keyfobs, PIN codes and QR codes, smartphones, and biometrics including facial recognition, fingerprints and iris scanning. Each has its own benefits and limitations.
Key Cards and Fobs
Key card access control systems comprise door readers that can read contact-based or proximity cards and fobs. The cards store user information, which the card reader can pick up and compare with authorized user credentials stored in the cloud; or an on-premise machine (for older systems). The use of keycards is still growing, driven by their advantages over metallic keys. However, modern offices and buildings are opting for cloud-connected mobile and facial recognition credentials because of the limitations of key cards and fobs.
Advantages
- Convenient: Contemporary and convenient for the end user.
- Trackable: You can monitor who entered the workplace at what time.
- Affordable: Low initial cost, although the long-term costs of printing and mailing cards must be considered.
- More Secure than Metallic Keys: You don’t need to worry about lost or stolen keys, although cards can also be lost, stolen or cloned.
Limitations
- Inefficient: Lost or forgotten keycards increase the operational burden and cost.
- No Remote Management: Most keycard systems run on local machines, so you cannot issue, revoke or change access permissions without going to the office
- No temporary access for visitors and deliveries.
- Not Scalable: Key cards that run on local networks cannot be used for multi-office locations.
- Manual Updates: Key card systems need to be updated and maintained manually. Manual updates are time consuming and expensive
Mobile Access Credentials
The global mobile access control platform market is expected to grow from $175.57 million in 2021 to $782.01 million in 2027, growing at a 27.1% CAGR. The rapid adoption of mobile credentials is driven by benefits such as remote management, better security and touchless entry. Nevertheless, mobile access control systems also have certain limitations.
How Mobile Access Control Works
Using mobile apps, a smartphone is made to act like a proximity key card and can store credentials. Mobile access control readers can read mobile credentials just like card readers can read proximity cards. The only difference is that mobile devices actively transmit the credential using BLE and NFC technologies whereas keycards store the information passively. Mobile phones can be used to unlock the door by bringing them close to the reader and also by using mobile apps.
Deep dive: Guide to Mobile Access Control
Advantages
- Easy Management: You can easily manage access permissions from anywhere through mobile apps and browsers. No need to print and hand out keycards every time.
- Remote Unlock: Unlock the door from anywhere using the access control mobile app.
- Scalability: Being cloud-based, the system can be easily scaled to multiple locations and satellite offices without breaking the bank.
- Flexibility: Latest mobile access control systems work with keycards, fobs and PIN codes. Systems such as Swiftlane, also allow the use of facial recognition credentials and video intercom to access the building.
- Security: Mobile phones are not lost, forgotten at home or stolen as easily as key cards. Mobile credentials are harder to copy than key cards.
- Cost Effectiveness: Mobile credentials eliminate the need to print and replace key cards, reducing operational burden and cost.
- Efficiency: Using mobile credentials saves the time that your security staff has to spend on replacing lost or stolen cards.
- Convenience: Mobile access control is more convenient for managers and end users.
Limitations
- Battery Issues: Some access control mobile apps can drain the phone’s battery. Users can be locked out of the building if the battery is dead.
- Substandard Software: Users of certain mobile access control solutions complain about software glitches where the door remains locked despite pressing the unlock button on the mobile app.
- Internet Issues: Broadband blowouts and wifi woes can make your access control system unusable; unless it can operate on LTE.
Face Unlock
Face recognition access control emerged during COVID and has now become a big trend. The overall facial recognition market is expected to more than double in size by 2028. The technology is particularly effective for access control because it offers the ultimate convenience and security apart from a sophisticated entry experience.
Advantages.
- Easy Enrollment: You can enroll people remotely using the mobile app without lining them up at the door.
- Remotely Grant or Revoke Access: Use the intuitive browser or mobile app interface to change access permissions from anywhere.
- Value for Money: Luxury experience at the price of the key card systems.
- Higher Security: The best facial recognition access control solutions read faces in 3D, so it’s almost impossible to fool them.
- Higher Convenience: Users don’t have to fumble for fobs or cards and can easily access the workplace even when both their hands are full.
- Your Face is Your Key: It doesn’t matter if you lost your card or drained your phone’s battery. You’ll never be locked out.
- True Touchless Functionality: Just look at the face reader, and the door unlocks. You don’t have to touch anything, not even your phone.
Limitations
- Privacy Issues: Breaches of facial recognition data can increase the severity of identity theft, harassment, and stalking. Make sure you double-check the privacy and data security certifications of your provider.
- Quality Issues: Dated facial recognition technology and substandard systems can be prone to frequent errors and failures. Make sure you choose a quality provider.
Factor 3: Access Management Experience
Coming to the access control management experience, you basically have two options.
On Premise Traditional Systems
The access control software runs on an on-premise computer. Legacy key card, fob and PIN based systems are usually on-premise systems. They are inefficient and inconvenient to manage for the following reasons:
- Burden: Card and fob based systems are a consistent workload on your security and front-desk employees. People lose or forget their cards at home all the time. To maintain tight security, lost or missing cards have to be canceled immediately and replaced with new cards.
- Insecurity: PIN codes can be forgotten or shared. They do not tether the credential to a particular person’s identity. Anyone can access the office using someone else’s PIN code. They can be a looming threat for your employees and security team.
- Inflexibility: Most card-based systems cannot be managed remotely. You have to go to the computer on which the system is running whenever you need to issue or revoke cards or change access permissions
These and many other limitations make these systems less suitable for modern workplaces compared to cloud-based systems.
Cloud Based Systems
Most new access control systems are cloud based. They are also called ACaaS (Access Control as a Service) solutions. The access control software and user data are stored in the cloud. On-premise components such as readers, controllers and hubs are connected to the cloud through wired or wireless internet gateways. Cloud access control has many advantages over its predecessors, with far fewer disadvantages.
Advantages
- They can be managed remotely through mobile and desktop devices
- You can add or remove people easily and quickly
- You get automatic software updates, security patches, and new features
- Simpler to use, thanks to native and intuitive user interfaces
- Cloud solutions have a lower TCO compared to on-premise systems
Limitations
- The only potential disadvantage is that these systems have to be connected to the internet to work. However, you can store a copy of data to work as a backup in case of internet outage.
Factor 4: Combining Occupant Access with Visitor Access
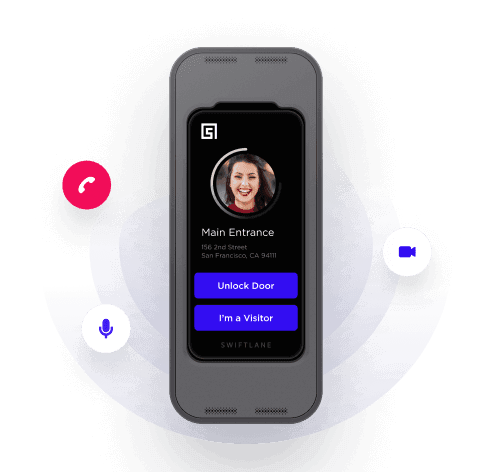
Until a few years ago, companies had to use different systems for visitor management and access control. This led to duplication, complexity and time wastage. Today’s all-in-one ACaaS solutions enable your building’s occupants to easily receive visitors and package deliveries using the same system that they use to access the premises themselves. Some of the features to look for include:
- Ability to issue temporary access codes, such as QR codes, pins or links
- Video intercom system to speak with visitors
- Receive video calls on mobile phones inside and outside the building
- Remote door release via mobile and landline phones
Meanwhile, residents or tenants can continue to access the building using facial recognition, mobile, card or PIN credentials.
Factor 5: Multi-Location and Hybrid-Office Access
Hybrid work models are already used by 63% of high-growth companies. The new model of work entails that workers balance their time between at-home and in-office work. Roughly speaking, some employees will work at home for 2 or 3 days a week and work from the office for the remaining part of the week.
The new work culture is inducing enterprises to open multiple smaller locations in different areas of a city to enable their remote employees to work from a physical office for a part of their week. If your office follows a hybrid model, your physical access control system should be able to support your employees. Here are the features you should look for:
- Control and manage access for individual doors across multiple distant offices
- Remote locking and unlocking features for managers and each employee or resident
- Programmable timed access for different offices and individuals following different working hours
- Easy self-management features for users and security teams
Latest stats reveal that 74% of US companies are using or plan to adopt a permanent hybrid work model, so this factor is seriously worth considering.
Additional Factors to Consider
Here are some more factors that merit consideration in 2023.
Integrations
Cloud based ACaaS (access control as a service) solutions should integrate with a variety of property tech including identity management systems, smart voice assistants, smart locks, video surveillance and more. Depending on your needs, you may look for built-in video intercom, facial recognition, and video surveillance features to avoid time-consuming and expensive third-party integrations.
Total Cost of Ownership
The TCO includes the direct and indirect costs associated with the system. A system may have a lower initial cost but may turn out to be more expensive when you factor in the cost of maintenance, training, and the time wasted in managing the system.
Customer Services
In case you are going for a cloud-based solution, make sure the provider you work with can provide hassle-free and reliable services to maintain and upgrade the system when needed.
Learning Curve
A system that is complex to use and requires weeks or months of training is probably not the best system to buy in 2023.
Upgrade Your Building Security
Get in touch with a Swiftlane specialist for more information on the best access control and video intercom solution for your building.